MAL“标准库”
- alias-hacks
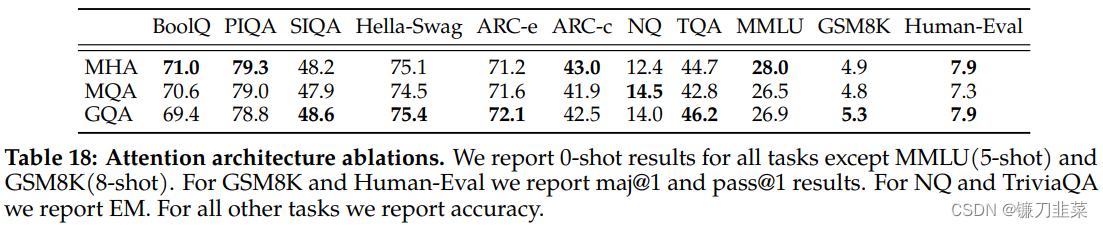
- benchmark
- equality
- load-file-once
- memoize
- perf
- pprint
- protocols
- reducers
- test_cascade
- threading
- trivial
alias-hacks
aliases for common clojure names to mal builtins
let/when/def/fn/defnpartial
benchmark
benchmark
An alternative approach, to complement perf
equality
This file checks whether the = function correctly implements equality of hash-maps and sequences (lists and vectors). If not, it redefines the = function with a pure mal (recursive) implementation that only relies on the native original = function for comparing scalars (integers, booleans, symbols, strings, keywords, atoms, nil).
scalar-equal?
Save the original (native)=as scalar-equal?mal-equal?
This implements = in pure mal (using only scalar-equal? as native impl)
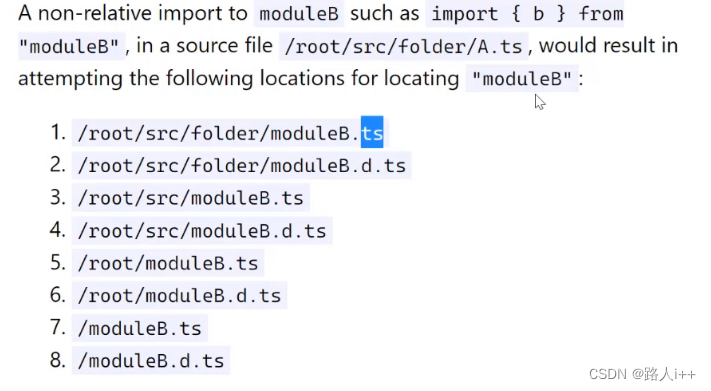
load-file-once
load-file-once
Like load-file, but will never load the same path twice.
memoize
Memoize any function.
memoize
Implementmemoizeusing an atom (mem) which holds the memoized results (hash-map from the arguments to the result). When the function is called, the hash-map is checked to see if the result for the given argument was already calculated and stored. If this is the case, it is returned immediately; otherwise, it is calculated and stored inmem.
For recursive functions, take care to store the wrapper under the same name than the original computation with an assignment like(def! f (memoize f)), so that intermediate results are memorized.
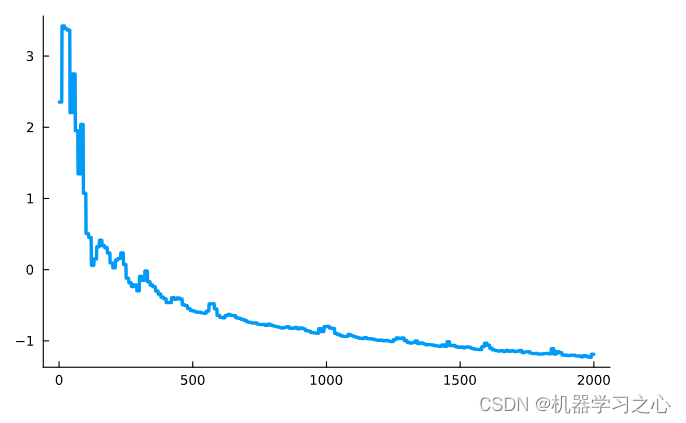
perf
Mesure performances.
time
Evaluate an expression, but report the time spentrun-fn-for
Count evaluations of a function during a given time frame.;; fn : function without parameters;; max-secs : number (seconds);; return : number (iterations)
pprint
pprint
Pretty printer a MAL object.
protocols
A sketch of Clojure-like protocols, implemented in Mal.
find-type
This function maps a MAL value to a keyword representing its type.
Most applications will override the default with an explicit value for the:typekey in the metadata.defprotocol
A protocol (abstract class, interface…) is represented by a symbol.
It describes methods (abstract functions, contracts, signals…).
Each method is described by a sequence of two elements.
First, a symbol setting the name of the method.
Second, a vector setting its formal parameters.
The first parameter is required, plays a special role.
It is usually namedthis(self…).
For example,
A protocol is an atom mapping a type extending the protocol to another map from method names as keywords to implementations.(defprotocol protocol(method1 [this])(method2 [this argument])) ;; can be thought as:(def! method1 (fn* [this]) ..)(def! method2 (fn* [this argument]) ..)(def! protocol ..) ;; The return value is the new protocol.extend
A type (concrete class…) extends (is a subclass of, implements…) a protocol when it provides implementations for the required methods.
Additional protocol/methods pairs are equivalent to successive calls with the same type.(extend type protocol {:method1 (fn* [this] ..):method2 (fn* [this arg1 arg2])})
The return value isnil.satisfies?
An object satisfies a protocol when its type extends the protocol, that is if the required methods can be applied to the object.
If(satisfies protocol obj)with the protocol below then(method1 obj)and(method2 obj 1 2)dispatch to the concrete implementation provided by the exact type.
Should the type evolve, the calling code needs not change.
reducers
Left and right folds.
reduce
Left fold (f (… (f (f init x1) x2) …) xn)foldr
Right fold (f x1 (f x2 (… (f xn init)) …))
The natural implementation forfoldris not tail-recursive, and the one based onreduceconstructs many intermediate functions, so we rely on efficientnthandcount.
test_cascade
Iteration on evaluations interpreted as boolean values.
or
(or x1 x2 .. xn x)is almost rewritten as(if x1 x1 (if x2 x2 (.. (if xn xn x))))except that each argument is evaluated at most once.
Without arguments, returnsnil.every?
Conjonction of predicate values (pred x1) and … and (pred xn)
Evaluate(pred x)for eachxin turn. Returnfalseif a result isnilorfalse, without evaluating the predicate for the remaining elements. If all test pass, returntrue.some
Disjonction of predicate values (pred x1) or … (pred xn)
Evaluate(pred x)for eachxin turn. Return the first result that is neithernilnorfalse, without evaluating the predicate for the remaining elements. If all tests fail, return nil.and
Search for first evaluation returningnilorfalse.
Without arguments, returnstrue.
threading
Composition of partially applied functions.
->
Rewritex (a a1 a2) .. (b b1 b2)as(b (.. (a x a1 a2) ..) b1 b2)
If anything else than a list is found where(a a1 a2)is expected, replace it with a list with one element, so that-> x ais equivalent to-> x (list a).->>
Like->, but the arguments describe functions that are partially applied with left arguments. The previous result is inserted at the end of the new argument list.
Rewritex (a a1 a2) .. (b b1 b2)as(b b1 b2 (.. (a a1 a2 x) ..)).
trivial
Trivial but convenient functions.
inc/dec/zero?/identitygensym
Generate a hopefully unique symbol.